Claude Computer Use: The New Era of Autonomous Computer Tasks
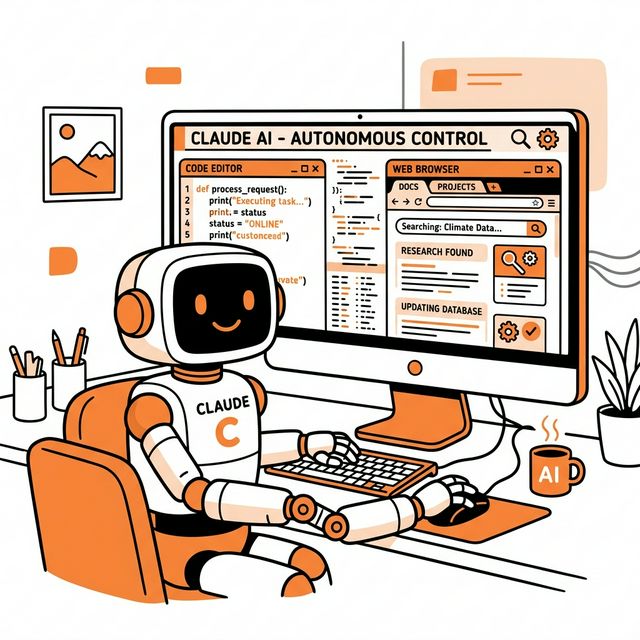
Anthropic has expanded its Claude AI with powerful “Computer Use” capabilities, allowing the AI to interact with your computer’s interface and perform various tasks autonomously by clicking, scrolling, and typing akin to a human user.
Contexto
Unlike traditional APIs that expect clean text-based communication or structured API endpoints, the new “Computer Use” beta enables Claude 3.5 Sonnet to interact directly with the desktop environment. The technology functions by taking continuous screenshots of the user’s desktop, using visual recognition to locate UI elements, executing precise mouse movements, and inputting text via the keyboard. This move signals a much broader push by Anthropic to develop AI agents that can “do work” rather than just converse.
Detalhes
When tasked with a goal, Claude utilizes an “agent loop” to navigate. It evaluates the current screen state, determines which tool or action to employ next, tracks its progress, and continuously corrects its course until the task is complete. It bridges the gap for software and tools that lack official APIs.
Key capabilities include:
- Desktop Navigation: Opening files, managing documents, and operating web browsers natively.
- Development Operations: Running development tools, actively making changes within IDEs, submitting pull requests, and initiating tests.
- Workflow Automation: Handling repetitive manual data entry, event planning, or scanning complex visual documents across multiple applications.
This feature integrates alongside Anthropic’s newer offerings like Dispatch (a mobile interface that lets you assign desktop tasks to Claude on-the-go) and Claude Cowork (for autonomous enterprise knowledge work). To ensure safety, Anthropic adopted a “permission-first approach,” where Claude requires user consent before engaging with entirely new applications and can be immediately halted at any time, adding a necessary layer of protection against potential prompt injection attacks.